Australian & New Zealand Distributors for:

IMAC
- Overview
- Sentinel
- Additional Modules
- Sentinel Lite
- Xpert
- Xpert for Excel
- Custodian
- Services
- Customers
- Review
CBM Services
- CBM Overview
- Services Provided
- Vibration Analysis
- Infrared Thermography
- Ultrasonic Detection
- Oil Analysis
Links
IMAC
IMAC Overview | IMAC Sentinel | IMAC Sentinel Additional Modules | IMAC Sentinel Lite | IMAC Xpert | IMAC Xpert for Excel | IMAC Custodian | IMAC Services | Customers | Review
IMAC Custodian
Record Alarm Overrides and Inhibits
The UK Health & Safety Executive’s Hazardous Installations
Directive states,
“Logic systems are likely to incorporate provisions for overrides,
for which there should be suitable management control arrangements. Procedures
should be available which detail the operation of the protective system including,
Override management (authorisation, security, recording, monitoring and review
of overrides, reset requirements).”
With the IMAC Custodian Override and Alarm Suppression Logbook, operators
can enter alarm overrides and inhibits into a secure web enabled database
eliminating the need for a paper logbook.
Designed to run on a network or ‘stand alone’, the simple browser
interface and Oracle database ensures secure storage and rapid data retrieval
at all times, thereby improving overall alarm management and reporting processes.
Key Features
• Reduces human error
• Enforces company strategy and procedures
• Simplifies administration
• Improves audit trails
• Enhances compliance
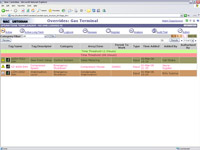
Screenshots |
IMAC Custodian is a web-enabled tool designed specifically to assist plant operators to manage their safety system procedures more effectively.
Simple Navigation
The Override & Alarm Suppression Logbook has a simple icon driven menu, allowing even the most inexperienced operator to quickly access information and view all overrides or suppressed alarms which are currently active. Completely intuitive, the package provides the operator with a simple yet reliable means of tracking and controlling plant inhibits whilst managing alarms in accordance with industry best practise.
Unique User Login
Every logbook Operator is assigned a unique 4 character PIN. This acts as a ‘digital signature’ which must be typed in before any entry will be accepted. With millions of different character combinations secure access is assured. As with a conventional paper logbook system, a supervisor must approve each inhibit made during that shift. In order to carry out this function, the supervisor must first login. As an added security feature the supervisor is automatically logged out after the shift (based on a predetermined time period), or if another supervisor logs in.
Improve Audit Trails
A key factor in the design of IMAC Custodian is its clear and simple audit trail display. Every action that takes place in the logbook is recorded here. Each entry has a unique consecutive ID number, and is in chronological order. It is not possible to edit entries in the audit trail, however they can be copied into other applications or documents.
Reduce Human Error
Integration with IMAC Sentinel automates much of the logbook procedure, this removes the risk of human error from these tasks, allowing operators to focus on more productive issues.
Perform Statistical Analysis
As well as performing the conventional logbook function, it can also perform statistical analysis on overrides and suppressed alarms based on time period, Safety Integrity Level and area of plant. Using these results the operations team can develop an effective strategy for reducing the use of such inhibits.
Contact us at [email protected] to arrange a demonstration.